

So good to finally have a label for what went wrong with Drupal!
Stranded major
Web developer. Lead developer of PieFed


So good to finally have a label for what went wrong with Drupal!
Stranded major


The homeless people living in RVs are the responsible and organized ones who saw a bad situation coming and invested in a solution that would keep them from living in a tent.
If that solution is taken off the table it’ll just lead to more people living in tents and all the problems that come from that.


This is getting complicated.


The only large mainstream competitor, which would probably benefit from github’s troubles: “We saw github breaking itself regularly because of it’s own slop coding AND flooded with trash vibe coded projects and thought - that’s where we wanna be!”


Maybe they’ve blocked you.


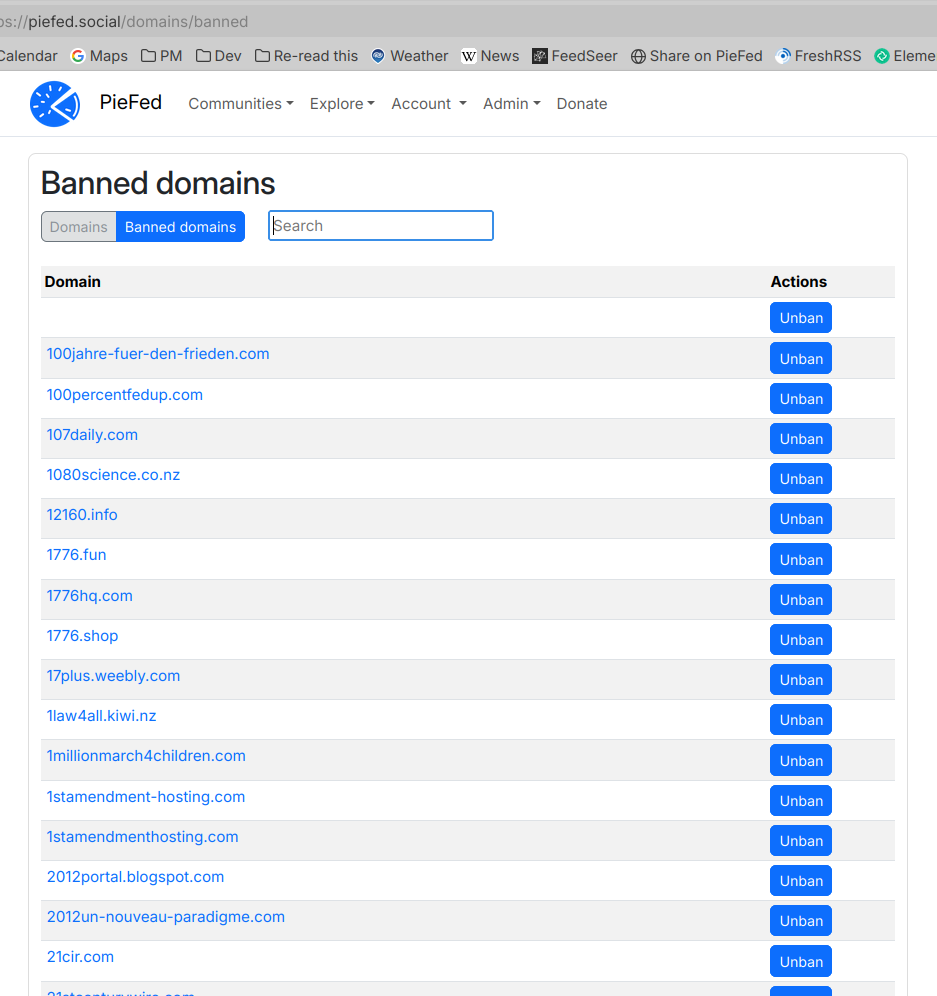
If they want to click 3000 buttons, yes. These buttons are not new functionality, it’s been like that since the beginning.
Easier just to empty the relevant database table! It’s called ‘domain’ if anyone in the future finds this.


Here is the user interface for unblocking:


Thank you for that, I’ll think about it.


This is a strong and succinct argument, cheers.
We need peoplesdispatch.org I think it’s valuable thing to have a take on events from their angle. Yet it needs to be read with an understanding that they have an angle. Using the warning icon to provide that understanding is clunky and wasn’t really intended for that purpose. There has been some drift in the usage away from the original idea behind the feature.
One day it might be good to have a different icon for providing context, separate from providing warnings.


I don’t believe software can be neutral. By making banning them equally easy as not, we’re saying that those choices are of equal worth - doing that is taking a side and it’s the side of giving fascists an easier way in. Nope! That’s how Mastodon gets forked into Truth Social.
Interesting how this thread started out about me being too right wing and now for other people it’s about me being too left wing. Heh.
Can’t please everyone and I’m not trying to.


Fork PieFed and remove the 4 lines of code involved in doing this, then. See cli.py, line 160.
IDGAF.


It depends on your definition of easy. Here is the admin UI for unbanning domains.
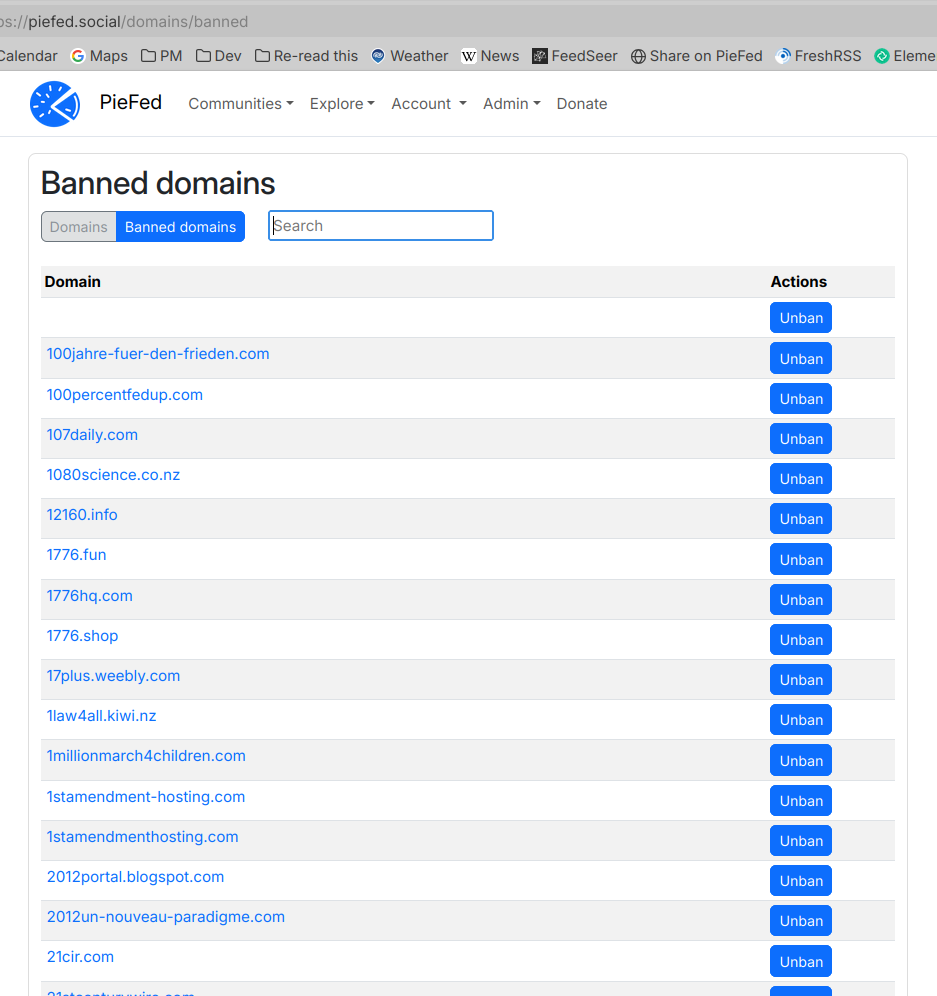
Also they can go into the database and empty the domain table.


I don’t want fascists to benefit from my work. But it’s FOSS, so anyone can download and install it, so I made it extremely unattractive to fascists.
There are plenty of other places where people can have “free speech”.
Facebook, or reddit, for example. /s


I’m happy to explain. You could have just asked, though.
During initial installation PieFed downloads a big list of 3000 right-wing domains from https://github.com/rimu/no-qanon and blocks them all. Admins can unblock them if they want but they would need to do them individually so I bet none do.
The list includes things like fox news, breitbart, etc. Before starting work on PieFed I spent 3? years studying right wing disinformation - qanon, antivax, all that and that blocklist is an output from that. Every site on that list was reviewed personally.
So.
Additionally, I have manually added these warnings (not blocks) onto some domains, for piefed.social only. You can download a list of those warnings from https://join.piefed.social/wp-content/uploads/2026/05/warnings.ods
Most of them are tabloids, AI slop farms and a handful are authoritarian government mouthpieces.
So there’s 3000 right wing sites that simply can’t be linked to and 47 sites with warnings, about 10% of which are left wing. There’s no need to warn for fascism because posts that link to them are not displayed in the first place.
There’s an ideological slant to PieFed for sure, and it’s very much in favor of the left. That could be why maga.place and lemmychan.org use Lemmy and not PieFed.
I’ll take another look at peoplesdispatch and see if there’s a less triggering warnings I can put on it.


That’s interesting.
How much ram did it use while running?
If you used a GPU, how much does it cost in today’s prices?


Hell yeah


How the hell does an article that we can’t even read get so many upvotes.
Stuff like this really shakes my belief in the voting system.
The numbers are the bottom of this graph are the hour, in UTC. So 3 = 3 AM.
Looks like the quietest time is about half as active as the peak.