

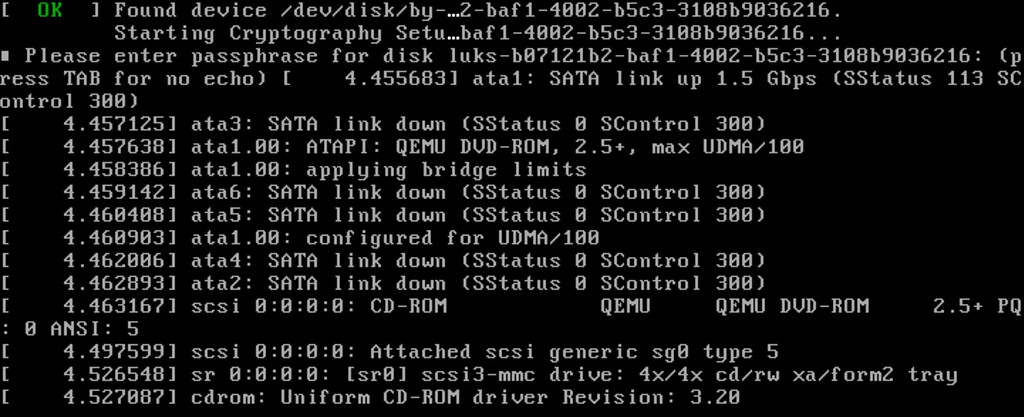
They messed up the signing on the server side.
They are using all non-stable technology. The Github action and cosign may be normal, but Fedora doesnt release their container images (even though they are the ones that uBlue consumes).
The updating mechanism is fine, this is a security measurement. If the signing failed, it shouldnt update as this could mean malware.











Thanks! Really helpful!