In the last couple of weeks, I’ve started getting this error ~1/5 times when I try to open one of my own locally hosted services.
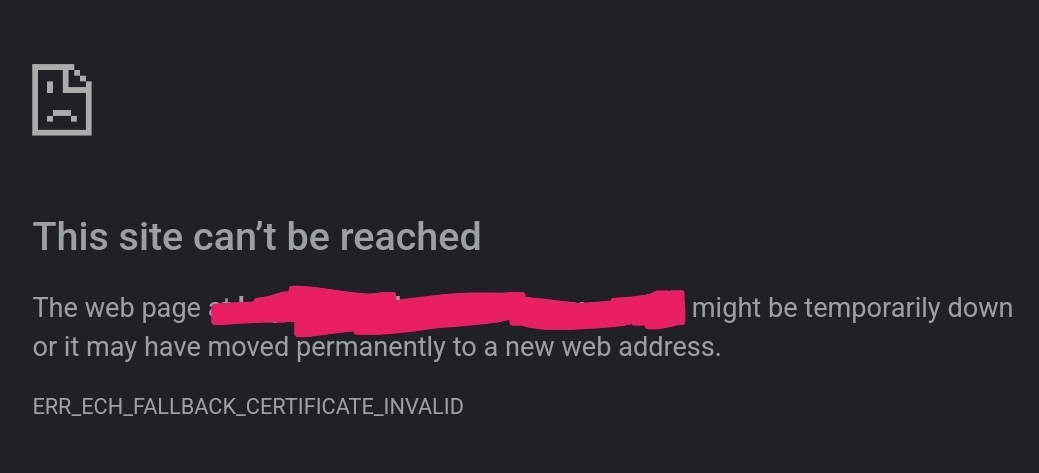
I’ve never used ECH, and have always explicitly restricted nginx to TLS1.2 which doesn’t support it. Why am I suddenly getting this, why is it randomly erroring, then working just fine again 2min later, and how can I prevent it altogether? Is anyone else experiencing this?
I’m primarily noticing it with Ombi. I’m also mainly using Chrome Android for this. But, checking just now; DuckDuckGo loads the page just fine everytime, and Firefox is flat out refusing to load it at all.
 Firefox refuses to show the cert it claims is invalid, and ‘accept and continue’ just re-loads this error page. Chrome will show the cert; and it’s the correct, valid cert from LE.
Firefox refuses to show the cert it claims is invalid, and ‘accept and continue’ just re-loads this error page. Chrome will show the cert; and it’s the correct, valid cert from LE.
There’s 20+ services going through the same nginx proxy, all using the same wildcard cert and identical ssl configurations; but Ombi is the only one suddenly giving me this issue regularly.
The vast majority of my services are accessed via lan/vpn; I don’t need or want ECH, though I’d like to keep a basic https setup at least.
Solution: replace local A/AAAA records with a CNAME record pointing to a local only domain with its own local A/AAAA records. See below comments for clarification.


I do have external acces to Ombi via cloudflare; but the device I’m seeing this problem on is permanently connected to a VPN hosted from the same server machine as ombi/nginx with ‘block all connections without VPN’ enabled. And this testing has been done from within the same LAN.
It should never see/reach cloudflare for this service.
/edit; I’ve also disabled ‘use secure DNS’ in chrome. I host a local DNS within that lan/vpn network.
Try with nslookup and see if you’re resolving the domain to both your local ipv4 address, and the Cloudflare ipv6 at the same time. I am using pihole for my local DNS, and it would give me both my local address, and also the Cloudflare ipv6 address.
Edit
My pihole will ask upstream even if the domain was listed locally. It doesn’t ask Upstream for cname.
Crap, looks like that’s exactly what it is.
Now how to fix that…
Added an AAAA record to pihole:
ombi.mydomain.example 0000:0000::0000:0000
Now nslookup returns the correct ipv4 address, and ‘::’ as the ipv6.
We’ll see if that works.
That unfortunately did not work. I am only getting the ipv4 address now, but I still get the same ECH error in chrome 1/5 tries.
Firefox now changed errors from ‘invalid certificate’ to ‘connection is insecure but this site has HSTS’ (true). Still wont show the cert or provide any further info. (forgot to grab a screenshot before the below ‘solution’)
I’m really annoyed at this point and have just disabled cloudflare proxying for this service. That seems to have sorted it for all browsers. I may look further later, I may just say fuck it and leave it like this. Gotta walk away for a bit.
You should change to use cname in pihole. I will write up on my computer later for you.
Can you verify with wireshark that the traffic is only going through your lan? I’m not hip enough for nginx but I used to have to run apache under gdb all the time to trace random errors from the server. That would be next, if the traffic is really local.
I’ll look into that next if what I’ve done doesn’t work. (see other comments)